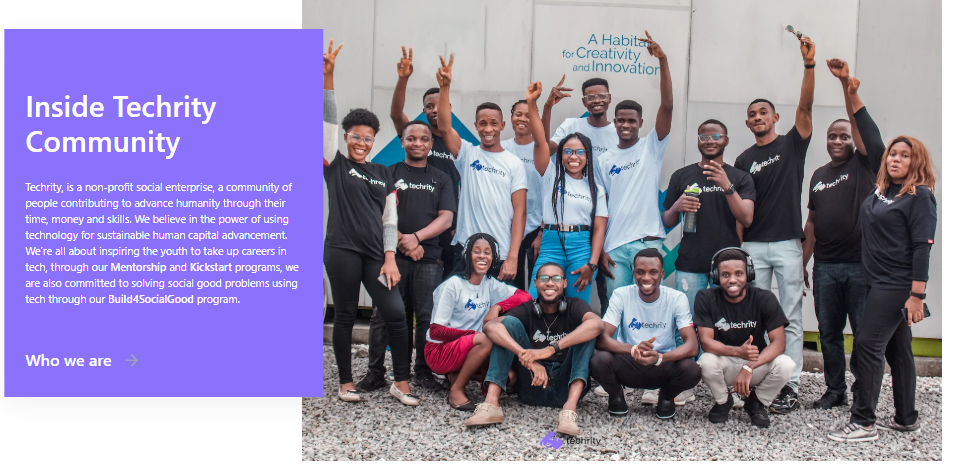
For half a decade, the Techrity Innovation Foundation has been on a steadfast mission to transform Africa’s digital landscape. What began in December 2020 has evolved into a continental movement dedicated to bridging the digital divide. On October 25, 2025, Techrity marked its 5th Anniversary by celebrating this journey of empowerment at the fourth edition of its flagship conference, themed AIMPACT Africa, held in Port Harcourt.
The milestone event brought together over 500 innovators, entrepreneurs, and educators to explore how Artificial Intelligence (AI) and emerging technologies can drive inclusion, digital literacy, and sustainable development across the continent.
Grassroots Impact: The Road to Tech for Good
Techrity’s commitment to “Empowering a Continent” begins in the classroom. Leading up to the anniversary conference, the team embarked on the “Road to Tech for Good” outreach, visiting Rumuokuta Girls Secondary School and Community Secondary School. The mission was to inspire young students to view technology not just as a subject, but as a critical tool for shaping their futures and solving real-world problems.
To solidify this commitment to early access, Techrity sponsored 120 students from public and private secondary schools across Rivers State to attend the conference. A powerful highlight of their participation was the emergence of Emmanuel Amaechi, an SS1 student from Christ Army Educational School, as the winner of the interschool Q&A session. He received a ₦50,000 cash prize and a full Tech Scholarship from Mr. Chinoso Chijoke, Founder of Cupid Technologies.
Key Takeaways: The Moments and Highlights That Shaped the Conference
Opening the conference, Islamiat Arinola Oseni, Senior Project Officer at Techrity, described Tech for Good as “more than an event, it is a movement to leverage technology for empowerment, community growth, and social impact.” She highlighted Techrity’s commitment to bridging the digital divide through mentorship, capacity building, and inclusion-focused initiatives.
Delivering the 5th anniversary speech and Impact story, Techrity’s Founder and Team Lead, Mrs Owanate Amachree, reflected on the foundation’s growth since its establishment in 2020. She said Techrity has evolved into “a pan-African force for social innovation and digital empowerment,” citing initiatives such as Hack for Good, the Techrity Mentorship Program, the Kickstart Initiative, and the Laptop Support Scholarship. “Technology has the power to redefine Africa’s growth narrative. At Techrity, we are building an ecosystem that enables learning, innovation, and impact,” she said.
The Keynote Sessions offered thought-provoking insights into the transformative power of technology in shaping Africa’s digital future. Mr Kenneth Nwokoro opened with “Building an Inclusive Digital Economy: Empowering Communities and Closing the Digital Divide,” emphasising the need for equitable access to technology and digital opportunities across all communities. Chimene Chinah followed with “AI for Inclusive Growth: Harnessing Artificial Intelligence to Drive Africa’s Transformation,” exploring how artificial intelligence can catalyse sustainable development and inclusive progress across the continent.
The Guest Speakers further enriched the discussions with practical perspectives on innovation and empowerment. Mrs Amarachi Stanley-Duru delivered a compelling session on “Shaping Africa’s Workforce for the Future: Embracing Digital Transformation and Skills Development,” highlighting the importance of upskilling and adaptability in a rapidly evolving world. Mrs Karla Obakpolor rounded off the segment with “Building for Social Good: Scaling Innovation and Creating Impact,” emphasising the role of purpose-driven innovation in driving meaningful change across Africa.
The Speaker Session featured Harmony Elendu, who delivered an insightful presentation titled “People Behind Models: How AI is Elevating Careers and Skills Expansion.” Her talk shed light on the human side of artificial intelligence, exploring how AI is transforming industries and empowering individuals to build new skills, enhance their careers, and thrive in the digital age.
The conference also featured engaging panel sessions, lightning talks and a fireside chat that explored innovation, inclusion, and Africa’s digital future. The first Panel Session focused on the topic, From Learner to Leader: Forging a Resilient Tech Talent Pipeline through Ecosystem Collaboration hosted by Bliss Isioma Ajie (HR/Operations Manager, Mently) and the Panelists were Richard Pepple (Founder, Technoville) and Shammah Nei (Director, Engineering Philanthrolab), The second Panel session focused on Navigating The New Financial Frontier: Regulation, Innovation and The Future of Crypto in Nigeria hosted Mr Godwin Jimmy (CTO, Dantown HQ) and the panelists were Godfrey Kelechukwu (Founder, Boardroom), Favourite Henry (Product Marketing Manager), Chininso Chijioke (Founder, Cupid Technologies), The Third Panel session focused on the topic, The Global Talent Playbook: Unlocking Remote Opportunities and Building a Competitive African Workforce, was moderated by Fano Oyin Jessica, Techrity’s Chief Administrative Officer. Panellists included Lloyd Otu, Co-Founder of TalentPoel, and Newton Adiari Newton, Product Manager at Cre8Space Africa, shared insights on remote work, digital tools, and how African youths can compete in a borderless economy.
The fireside chat with Julian Duru (ex Moniepoint engineer and now an independent researcher) hosted by Daniel Obiyo (Founder, Quint Impact Initiative), offered an inspiring story of resilience and leadership, as he discussed personal experiences and lessons from Africa’s evolving innovation space.
The Lightning Talk Breakout Sessions featured a series of simultaneous, high-energy presentations where speakers shared unique insights on technology, creativity, and artificial intelligence. Chibuzo Madumere explored “From Curiosity to Code: How AI and Creativity Empower Tech Beginners,” emphasising how innovation often begins with curiosity. Opuine Kayode Fowora presented “AI for Differentiated Instruction & Inclusivity: A Teacher’s Perspective on Empowering Every Learner with AI,” shedding light on AI’s role in inclusive education. Yves Kwameh V. delivered “Beginner Skills You’ll Need Before the Boots Take Your Briefs,” a dynamic talk on essential skills for those starting their tech journey. Numbere Tehila Tamunobakam discussed “Agentic AI and Liability: Who Bears the Burden When Mishaps Occur?” examining accountability in the age of intelligent systems. Meanwhile, Precious Sunday inspired attendees with “Unlocking the Future: Navigating Tech’s Uncharted Territory,” encouraging bold exploration of technology’s evolving landscape.
A key highlight of the event was the official launch of Made for Good, presented by Peculiar Akinloye, Techrity’s Operations Manager. Made for Good is a purpose-driven brand that embodies the spirit of paying it forward using proceeds from its merchandise and initiatives to support causes such as providing laptops, internet data, and digital tools for young Africans. The initiative also connects startups, organisations, and innovators working on technology-driven impact projects across the continent. According to Akinloye, the platform aims to “promote partnerships, shared learning, and scalable innovation for development.
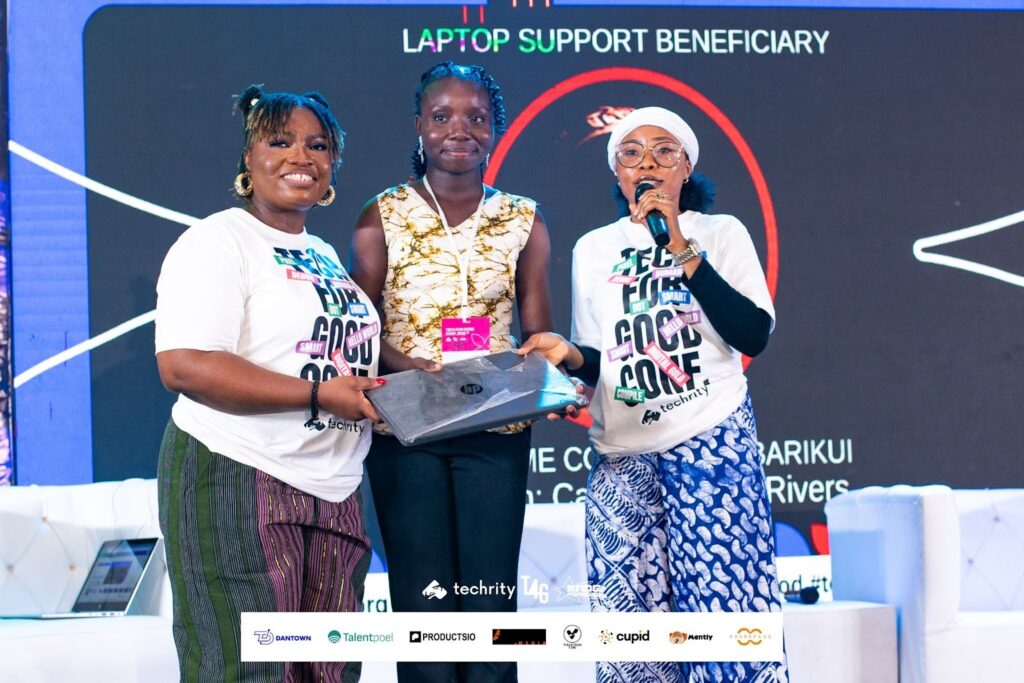
In addition, there was the Techrity Laptop Support Scholarship presentation. This initiative equips young Nigerians with laptops, internet access, and mentorship to enhance their digital skills and create career growth opportunities. Following a transparent selection process guided by passion, need, and commitment to social good, 11 (eleven) young Nigerians were awarded laptops, data support, and mentorship to boost their digital careers at the conference. Among these beneficiaries were Ikordeme Confidence Barikui, Onaeko Emmanuel Oladipupo, Ozuru Irenma Pearl, Ozuru Olanma Jewel, Philomena Nkereuwem Nyah, Iyke Victor Chidera, Winner Osinachi Offor, Elekwachi Zion Chibuchi, Emeka Victor Chigozie, Okonkwo Ckaima Peniel, and Ebubechukwu Osy-Uzoekwe. “We believe in using technology to transform lives, one person and one community at a time,” Oseni said.
Another major highlight of the day was the Techrity Social Impact Awards, which honours individuals and organisations using technology to drive mentorship, digital inclusion and social good. The award recipients included Renaissance Innovation Labs (Tech Community Partner of the Year), Kenneth Nwokoro ( Social Impact Award (Mentorship), Stakeholders Democracy Network (Social Impact Award – Tech for Gender Equality), Bright Chinenyeze (Social Impact Award (Digital Inclusion Advocate), Richard Sodienye Pepple (Social Impact Award – Mentorship), and Richard Tamunotonye (Social Impact Award – Mentorship).
A Five-Year Legacy and a Call to the Future
In just five years, Techrity has grown into a global community of 886 innovators with over 12,000 digital followers across Nigeria, Kenya, India, Botswana, Ghana, Rwanda, and Uganda. Through initiatives like the Kickstart Initiative, which has provided 35 laptops and ₦5 million in data support, and a mentorship program engaging over 100 participants, Techrity is actively nurturing Africa’s next wave of tech talents.
The success of the 5th anniversary celebration was bolstered by several partners, including Dantown (Key donor and partner for the Laptop Support Scholarship), Productsio, TalentPoel, Cre8Space, Artful Media, Cupid Technologies, Volunteers Crib, Mently, and Made for Good.
In her closing remarks, Owanate Amachree thanked all partners, speakers, and volunteers for their contributions, noting that “the true impact of Techrity lies not only in its social impact programs but in the lives we transform.” She reaffirmed the foundation’s goal to continue empowering Africans through technology, mentorship, and innovation — inspiring, coaching, and building for social good.
As part of its five-year milestone, Techrity is extending an open call to corporate partners, development organisations, startups, and philanthropists to collaborate in building the future of young Africans through mentorship, digital education, and social impact programs designed to bridge gaps in unemployment, inclusion, and opportunity across Africa.
Let us drive this mission together by equipping young people with laptops, internet access, and digital skills, fostering innovation through SDG-focused hackathons and mentorship programs, and promoting inclusion and gender equality through technology-driven education.
Organisations and individuals interested in partnering can reach out via hello@techrity.org or visit www.techrity.org to learn more.